By Aashka Dave, Claudia Chen, and Ethan Zuckerman Since the 2016 U.S. presidential election, news coverage of hate speech and mis/disinformation has skyrocketed. What was once a sleepy beat led by freelancers and activists has become a central topic of coverage for almost every news organization. As the news cycle […]
Blog
From legislation to implementation: Exploring how to prototype privacy bills through human-centered policymaking + design By Anna Chung, Dennis Jen, Jasmine McNealy, Stephanie Nguyen The rise of data privacy breaches and a look into policies that address these challenges “If a parent comes in and says, ‘Oh, I want to […]
My first sourdough starter was a dud, and I coveted my coworker’s. I had seen crusty masterpieces from Julia on the #bread channel. This was back in 2016, and after Julia enthusiastically shared her starter with me, I began caring for and baking my own boules. Google News has me […]
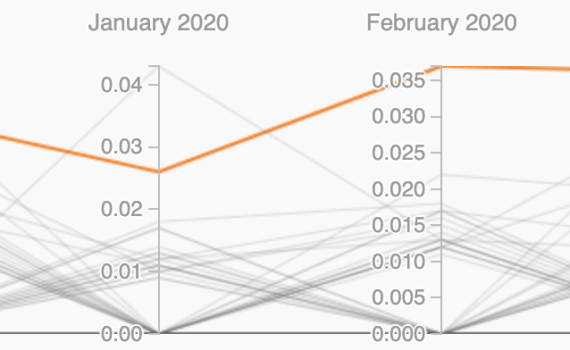
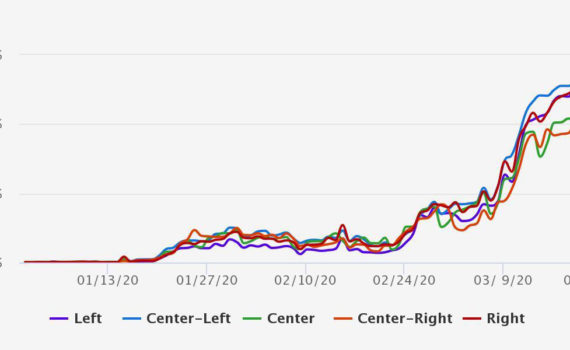
By Fernando Bermejo, Luigi Reggi, Simona Tiribelli, Ethan Zuckerman In US media, virtually every national or international news story is seen through a partisan lens. It’s reasonable to hypothesize that the novel coronavirus and COVID-19, the disease it causes, would follow a similar pattern. In particular, given President Trump’s attempts […]
It’s difficult to browse social media these days without seeing news on coronavirus. In fact, every other post seems to be related to concerns, updates, and memes about coronavirus — and with good reason. These are unprecedented times where a health crisis has taken place on a truly global scale, […]